Election Fraud is NOT a New Concern
For years there have been people sounding the alarm on election security, unless it’s in their favor. Funny how that works. We came across several documents found on various government websites, referencing the same type of issues and concerns we still have today.
Clint Curtis Admits to Creating Algorithm to Flip the Votes
Watch the video of Clint Curtis telling the story of how elected officials contacted him and hired him to create a vote flipping algorith. Then click the link below to learn more.
Learn more about Clint Curtis HERE.
Inspector General on Election Security:
“Computer-enabled election systems may be subject to cyber intrusion. The risks to computer-enabled election systems vary by county and jurisdiction, depending upon the types of devices, network architectures, information technology (IT) governance measures, and other protective measures implemented. For example, election infrastructure elements that are potentially vulnerable to cyber and physical intrusion include:

• Electronic Voting Systems – In laboratory testing environments, security researchers have repeatedly demonstrated that some voting machines are vulnerable to compromise, usually due to physical access to the machines, which could result in the manipulation of vote totals.
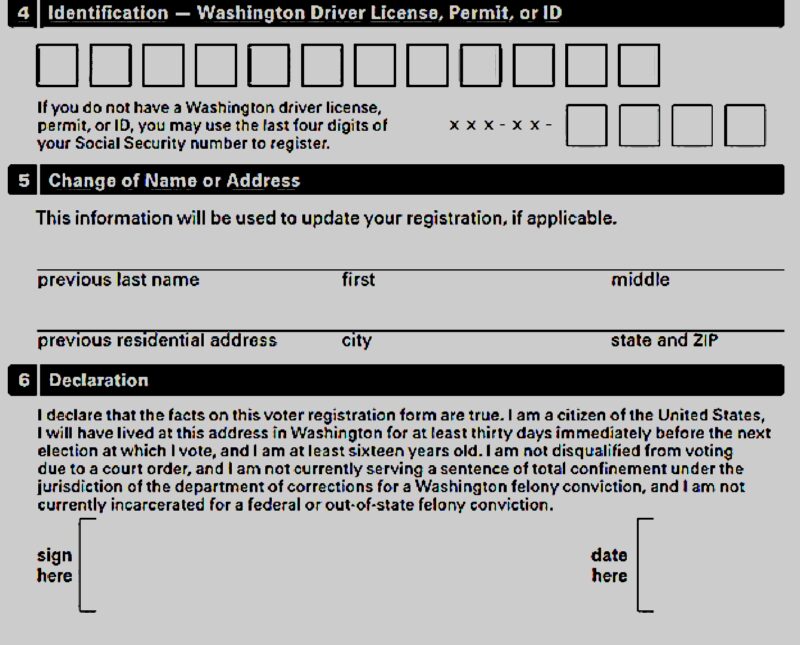
• Voter Registration Databases – Online voter registration systems may be vulnerable to cyber attackers seeking to gain unlawful access to voter registration databases.
• Public Dissemination of Voting Results – State governments’ information technology solutions generally include public internet connections to disseminate election results to the public and media on Election Day. Public internet use could result in inaccurate reporting on numbers of votes.”
Read the full report:
2016 Video re: hacking the voting machines
Ingalls Information Security Report
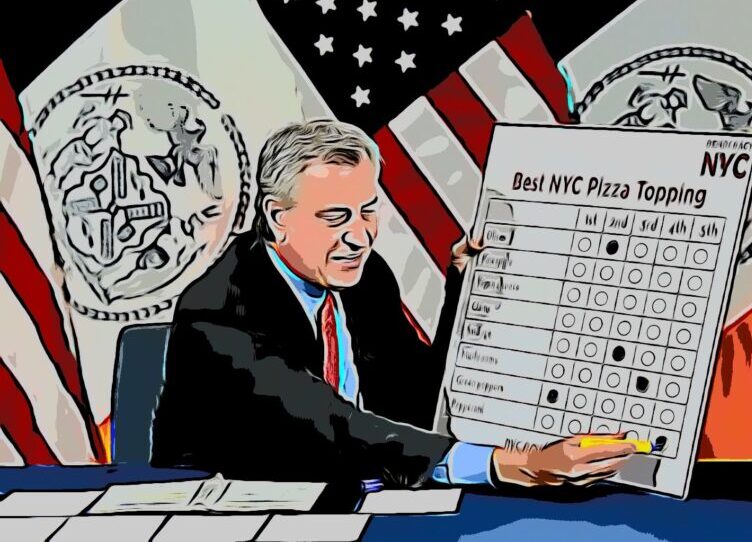
How the 2020 Presidential Election Could be Hacked January 2020:
IT Managed Service Providers (MSPs) and Remote Monitoring and Management (RMM)
Most local election officials and boards are not capable of staffing sufficient IT experts for in-house maintenance and system administration, and so the vast majority outsource their IT maintenance to small businesses called Managed Service Providers, or MSPs.
These MSPs employ about 15 employees on average1, and primarily support user help requests and maintenance efforts such as data backups, anti-virus updates, system patching, and firewall deployment. Unfortunately for MSPs, criminal groups targeted them heavily with ransomware in 2019, exacting a heavy toll MSPs use automation tools to scale their service delivery to as many customers as possible.

These automation tools are referred to as Remote Monitoring and Management (RMM), and there are lots of Web-based versions for MSPs to choose from. Because they are Web-based, anyone with an internet connection can log into them using a username and password.
This presents a serious security problem, because attackers who steal the login credentials for RMM tools can leverage those tools to deploy malware and ransomware to MSP clients and the MSP itself. At the time of this writing, none of the RMM tools we have reviewed require Multi-Factor Authentication (MFA) to be enabled.”
Download the full report below.
It’s No Secret